
Consensus Mechanisms for Permissioned Blockchain Protocols
Blockchain technology has gained a lot of interest as a result of its use in public blockchain networks like Bitcoin and Ethereum. Businesses who wish to benefit from blockchain technology while maintaining control over the network’s users and operations are increasingly turning to private blockchain networks, also known as permissioned blockchains.
Any blockchain protocol must provide consensus techniques to support the decentralized and trustless nature of the technology. Compared to public blockchain networks, private blockchain protocols have different requirements and necessitate alternative consensus mechanisms. In private blockchain systems, consensus methods are even more important for guaranteeing the network’s dependability and security. These networks are designed to be used in environments where security, privacy, and control are essential, like in financial or medical applications.
The range of access and control distinguishes private from public blockchain protocols. A private blockchain only allows a select few users to access it, in contrast to a public blockchain where anybody can join the network and confirm transactions. This is accomplished by establishing various access restrictions and permission requirements.
Why Is Consensus Vital for Private Blockchains?
Even when a private blockchain is controlled by a certain group of individuals, the integrity of the data must still be ensured. In this, consensus algorithms are utilized. This validation process protects the network’s security and legitimacy in private blockchain networks by restricting who can approve transactions and add them to the blockchain. This ensures network security, which is essential in industries handling sensitive data and exposed to malicious individuals or unauthorized access.
Consensus protocols enable the network to operate independently of any individual participant. This is crucial in industries like finance and healthcare where protecting the privacy of sensitive data is of utmost importance.
Even if a single company or group owns the majority of the nodes on a private blockchain, these strategies are crucial for maintaining the network’s reliability and confidence among the participating parties. It ensures that everyone accepts the ledger and that the network operates effectively and securely.
Since it ensures the network’s security, integrity, and anonymity, this validation mechanism is generally regarded as a crucial part of private blockchain protocols since it makes them suitable for use in sectors requiring a high level of trust and control.
Permissioned Protocols: How Do They Achieve Consensus?
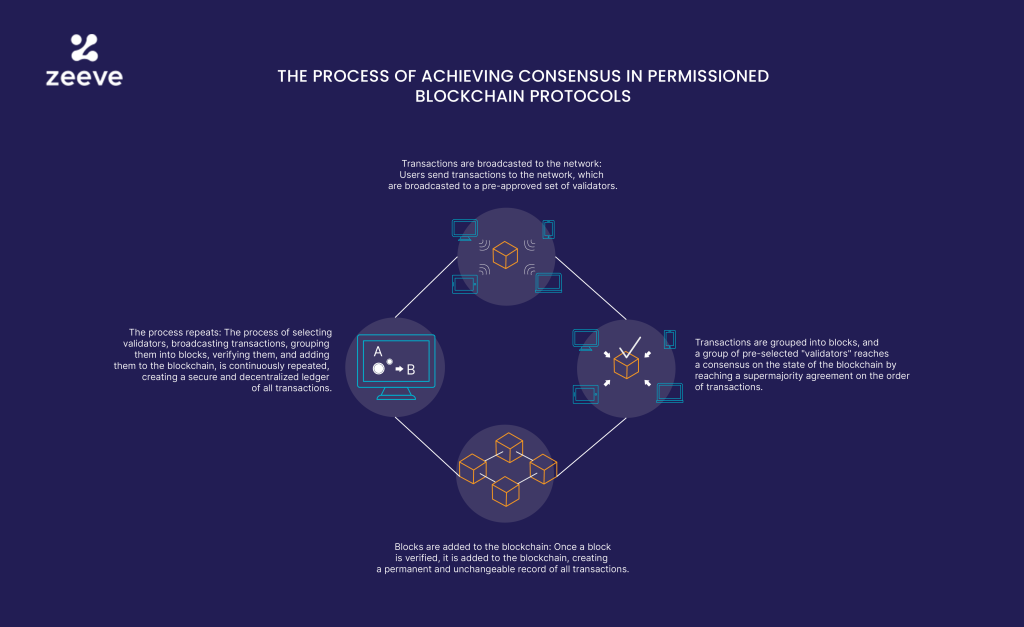
In permissioned protocols, consensus is reached through a planned process involving a pre-selected set of validators. Transactions are first broadcast to the network by users, who then have the pre-selected validators verify them. These transactions are compiled into blocks, and a group of validators agree by a supermajority on the order of transactions to reach a consensus regarding the state of the blockchain.
After a block has been verified and uploaded to the blockchain, a permanent and unchangeable record of all transactions is kept there. Through this continual process, a secure, decentralized ledger of all transactions is produced.
As opposed to permissionless protocols like Bitcoin and Ethereum, permissioned protocols have a pre-approved group of validators. These validators, who are responsible for protecting the network’s integrity, are often chosen by the organization that established the protocol. As a result, they are in charge of confirming transactions, gathering them into blocks, and reaching an agreement on the state of the blockchain at the moment.
Using pre-approved validators in permissioned protocols increases network security since they are well-known organizations and are held accountable for their conduct. In contrast, permissionless protocols allow anyone to participate as a validator and make it more challenging to identify and hold malicious actors accountable.
The steps are repeated to build a secure and decentralized log of all transactions: choosing validators, broadcasting transactions, arranging them into blocks, validating them, and adding them to the blockchain.
Protocols of Consensus for Allowed System
The current permissioned blockchain systems offer a wide range of consensus processes. These consist of:
Proof of Authority (PoA)
Identity serves as the sole source of authority verification in the Proof of Authority (PoA) consensus method, which uses it to verify transactions. When the identities of the validators are known and have already been confirmed by the network’s governing body, it is widely employed in private and consortium blockchain networks.
In a PoA network, validators are typically people or organizations who have been granted the go-ahead to validate network transactions after undergoing due diligence. These validators are in charge of maintaining network security by making sure that only legitimate transactions are uploaded to the blockchain.
The two most well-known PoA-based permissioned blockchains are Quorum and Hyperledger Besu.
Evidence of Time Spent
Also known as The Proof of Elapsed Time (PoET) consensus technique validates transactions using a random waiting time algorithm. It is also used in private blockchain networks where the member nodes are reliable and whose existence is known.
Every node in the PoET network must hold idle for a certain period of time that is randomly selected. The right to begin work on the following block is given to the first node to successfully complete the waiting period. This waiting time can be determined similarly to a lottery, where the node with the lowest number wins, by using a trusted execution environment (TEE), which generates a random number and ensures that each node waits the same amount of time.
The Hyperledger Sawtooth Proof of Elapsed Time (PoET) consensus method solely provides economic analysis for resource-efficient mining (REM).
Practice of Byzantine Fault Tolerance (pBFT)
The main node, also known as the leader, in pBFT is in charge of gathering and allocating trades. The transactions that the leader has proposed are examined by validators, also referred to as backup nodes. A transaction is confirmed, verified, and added to the blockchain after being confirmed by a supermajority of validators.
The key advantage of pBFT is that it can quickly reach an agreement even while some nodes are behaving strangely. Before a transaction is confirmed, nodes must communicate with one another over at least three rounds of communication called “pre-prepare,” “prepare,” and “commit.”
However, once a block has been confirmed, it is said to be irreversible, which implies that any transaction included in it cannot be changed or undone. Even in the presence of malfunctioning nodes, the system will concur on a single block because of the safety feature of PBFT.
It is still plagued with issues. It takes more resources than other consensus algorithms and necessitates extensive communication between nodes. Furthermore, if a sizable number of the nodes are hacked, pBFT-based networks are more likely to fracture and become more vulnerable to assaults.
Hyperledger Fabric and Corda are the two most well-known blockchains that use PBFT.
Federal Byzantine Convention (FBA)
A distributed network can figure out its state by using the Federated Byzantine Agreement (FBA) approach to come to consensus among its nodes. As the network’s backbone, its Byzantine fault tolerance (BFT) algorithm enables the network to function even when some nodes are corrupted or malfunction.
Each node in FBA selects a group of reliable nodes known as its “quorum slice,” which may link to create a bigger “quorum” if necessary. The system’s state is then decided by the quorum. FBA is regarded as a decentralized consensus technique because quorums are established based on the preferences of individual nodes.
Well-known permissioned blockchain R3 Corda makes use of the Federated Byzantine Agreement (FBA).
Istanbul BFT
A consensus algorithm for private blockchain networks is called Istanbul BFT (IBFT). Because it is built on the Byzantine Fault Tolerance (BFT) algorithm, the network can continue to function normally even if some nodes are compromised or malfunction.
IBFT has two different categories of entities: validators and proposers. To create a block that is broadcast to the validators, the proposer must gather transactions from the transaction pool. There are two methods for choosing the proposer: round-robin scheduling or a sticky proposer, in which the same proposer is chosen for a predetermined number of rounds.
The block is then assessed by validators, who confirm that it complies with the network’s established policies and standards. A block is uploaded to the blockchain once it has been approved by more than two thirds of validators.
In a network of N validator nodes where N = 3F + 1, the system can accept nodes with up to F defects. This is due to the fact that a block cannot be regarded as legitimate unless it receives 2F + 1 validation messages from other validators. This makes it so the network can still agree on the system’s condition even if some nodes fail.
State-machine replication is carried out by Istanbul BFT on the Quorum blockchain and Hyperledger Besu.
Final Thought
The decision to choose a consensus mechanism for an enterprise solution is crucial and will depend on the project’s specific requirements and use case. Scalability, security, interoperability, and regulatory compliance are all important considerations when selecting a consensus method. The best choice will depend on the requirements for the specific project.
If you are still unsure about which permissioned protocol would be most effective for your use case or if you have any other questions about the procedure for choosing the right consensus, don’t hesitate to get in touch with Zeeve. You can rely on our team of experts to provide you with the information you need to choose wisely for your enterprise solution






Responses